A lot of people have asked me for some super simplistic examples of Zero Trust (ZT) and why it matters. So, I have decided to create a quick explanation.
Zero Trust is a very flexible framework that should be implemented in every technical system you employ. There is no one and only "best way" to implement ZT; there are lots of different products and services that can help you implement a Zero Trust structure in unique ways. Having some ZT layers and processes in place is better than nothing as these processes serve to slow down a hacker, hopefully giving you enough time to prevent a security breach.
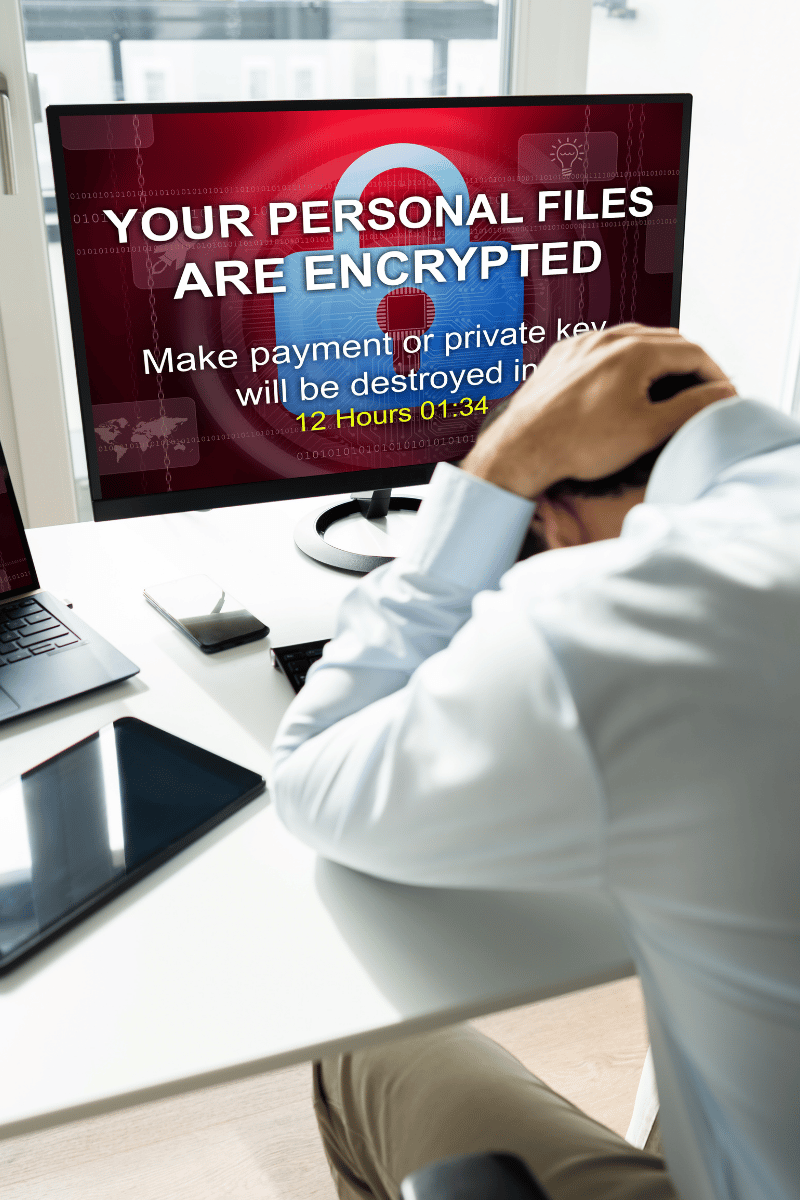
Most breaches (99%+) start on an endpoint device such as a computer or mobile device. The hackers will then steal the users’ login credentials, convince them to click on something, find a bug in the operating system to exploit, or physically hack the computer by plugging a flash drive or some other boot device into the machine. Next, they upload their remote access and other hacking tools which allows them to jump from PC to PC, or even to your local or cloud-based servers. From there, they will destroy your backup data, download all your important files to sell on the dark web, and encrypt your data to blackmail you to pay a ransom in exchange for the decryption key.
In a partial trust environment, it is easy for a hacker to achieve their goals. Intertwining with the common attack methods discussed in the previous paragraph, here is why a Zero Trust environment will mitigate the attacks and solve the problem:
- Password and credential theft allows the hacker to gain remote access to a computer, server, and any other device. Hackers can purchase lists of passwords from the dark web or send your users a phishing email that harvests their password. The hacker will then log in to their email or obtain remote access services.
A Zero Trust example that prevents this is Multi-Factor Authentication (MFA). This makes the hacker’s job much harder (but not impossible). When MFA is enabled, it provides an additional layer of identity verification and security by requiring the user logging in to input a temporary numerical pin. If the hacker does not have the user’s mobile phone or some other exploit to bypass MFA, they are stopped in their tracks.
- Hackers have historically been very successful at convincing a user to click on link or download a malicious attachment. Usually, they will impersonate a real person that the user is well acquainted with, such as a colleague or supervisor. The recipient usually thinks nothing of opening a file that was sent to them via email. Many exploits today cannot be detected by ordinary Anti-Virus software. Even Modern EDR’s (Next-Gen AntiVirus) can have trouble detecting new exploits that may have been just created today. They will allow the exploit to run, and by then the damage is already done.
A Zero Trust example would be to use a software tool to lock down and control what applications are allowed to run on any and all devices within the organization.
- In the case of physical attacks, there have been many reported cases of non-corporate owned devices being used as a vehicle to plug in and compromise a corporate-owned network. Other types of physical attacks can include impersonating or cloning a Multi-factor Authenticator; and in the most brazen of cases, hackers have dressed up as the cleaning crew or a AT&T technician to bypass any security to plug in their own equipment or use a flash drive to directly compromise a PC.
A Zero Trust example to potentially prevent this would be a combination of physical security processes like keypads and locks, an advanced firewall setup, and software tools to prevent these unfamiliar devices from registering on the network.
These are just a few examples of how to use a Zero Trust Framework to help protect your business. Security is constantly changing and as time goes on, new and potentially better methods may become available. To combat hacking and breaches, all businesses need to have a regular Cyber Security Assessment to be sure they are doing all that they possibly can to raise their level of Cyber Resilience. If you would like a complimentary Assessment, please fill out the form on this page, call us at 561-969-1616 or visit here.

More than 40 years ago, Chuck Poole set his eyes on one of the first "Personal Computers" commercially available and it was love at first sight. He was so enamored with computers that some people worried he might never do anything else - and they were absolutely right. Learn More.

You must be logged in to post a comment.