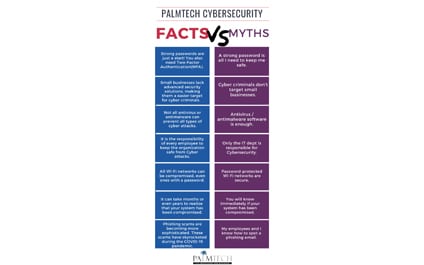
PalmTech Tips showing a few of the FACTS vs MYTHS
PalmTech Cybersecurity: Facts vs Myths
Learn why you should only visit HTTPS sites

Everyone uses the internet daily for a variety of reasons: to work, shop, or communicate with other people. Browsing the internet has become so commonplace that we often forget to check whether the websites we visit are safe. Let this serve as a reminder: a website can be deemed safe if the website’s URL has an “S” after the “HTTP.” Learn why that “S” matters.
Tips to Keep Your Business Data Safe

Losing or compromising data can be disastrous for your business. It can lead to reputational damage, costly lawsuits, and termination of contracts, among others. And because threats to data security are always present online, it's important to implement tough security measures that will keep your business data safe 24/7. Here are some tried-and-tested methods to safeguard your corporate data.
How Much Could A Ransomware Attack Cost You?
How to Avoid Phishing Scams and Scammers
Since the outbreak of COVID-19, there has been a universal trend of an increase in cyber-attacks as more people take their presence online for work and to connect with loved ones. As businesses transition to remote work and operations, cyber security and best practices are easily overlooked; creating the perfect opportunity for scammers to strike.
What Is Zero Trust In Cyber Security?
Use these tips to stay safe on Facebook and Twitter
Never let your guard down when you’re on social media! Malicious hackers are becoming better at stealing your personal information, so keep these reminders and tips in mind to remain safe while you’re on platforms like Facebook and Twitter.
Lock screens exist for a reason
Always lock all your devices as soon as you stop using them.
5 Security Issues To Look Out For
Cybersecurity is a constant battle, but there are significant steps you can take to keep your IT defenses strong and effective, one of which is to increase your knowledge of security threats. Here are five common ways your business systems can be infiltrated.
A Quick Refresher
What Are Managed Services, And Why You Should Demand This From Your IT Company
We all want to protect our businesses. They’re a part of who we are, and it would be devastating if anything bad happened — including an unexpected cyberattack. But it happens. Businesses are attacked every single day. Some businesses are left in ruin.